What Happens When Corrupt Judges & Election Officials Seal Entire Court Records Based on Fraudulent Concealment, Fraud Upon the Court, & “OFFICIAL MISCONDUCT”?
We have already experienced advocate judges creating their own law and holding their own court -
Here is a shot list of the activities of such advocate judges…
Chief U.S. District Judge James Boasberg, who ordered changes to grand jury rules after a Trump administration attempt to charge members of Congress and blocked deportations under the Alien Enemies Act.
U.S. District Judge Matthew Brann disqualified three Justice Department officials appointed by the Trump administration in New Jersey, characterizing their appointments as an “illegal power grab.”
U.S. District Judge Brian Murphy issued an injunction against the Trump administration’s move to stop recommending the COVID-19 vaccine for children and previously blocked the deportation of illegal migrants to “Safe Third Countries.” However, an appeals court later reversed this.
Judge Susan Richard Nelson ordered the release of an MS-13 gang member.
U.S. District Judge Royce Lamberth, a Reagan appointee, ordered the reinstatement of over 1,000 Voice of America employees, ruling that the Trump administration’s attempt to dismantle the agency was unlawful.
Judges have also intervened in cases involving immigration, student visas, and federal funding.
Other judges who have ruled against Trump include District Judge Jorge Luis Alonso, who granted a temporary restraining order against the administration to prevent the restriction of a police officer’s employment during an immigration case.
Judge Jamal N. Whitehead ruled that the Trump administration overstepped its authority when seeking patient data from a trans health provider.
Federal judges also blocked parts of Trump’s executive orders targeting law firms involved in the Mueller probe, citing potential violations of constitutional protections.
U.S. District Court judges have also issued nationwide injunctions blocking an executive order to end birthright citizenship, reinstating probationary workers, and blocking efforts to cut funding to the National Institutes of Health.
Supreme Court justices, including Chief Justice John Roberts and Trump appointees Amy Coney Barrett and Neil Gorsuch, ruled 6-3 against Trump’s global tariffs, stating he exceeded his authority under federal law.
The Supreme Court supported Justice Ketanji Brown Jackson’s arguments in blocking the Trump administration from revoking Temporary Protected Status for Haitian and Syrian immigrants.
Chief Justice John Roberts has publicly criticized personal attacks on federal judges, stating they are “dangerous” and “have got to stop.” His comments followed President Trump’s criticism of judges who ruled against his administration, including the Supreme Court’s tariff ruling and U.S. District Judge James Boasberg. Roberts has emphasized that while criticism of judicial opinions is acceptable, “personally directed hostility” is not.
The issue of judges blocking presidential actions has led some congressional Republicans to explore options to counteract what they perceive as activist judges hindering the Trump agenda, with some suggesting legislation to limit district judges’ power to issue nationwide injunctions.
But what if all the above, and those not mentioned here,
Are just the beginning?
It stands to reason that when any advocate wins by their deceptive and divisive means, they get hungry for more.
Evil ALWAYS works that way, righteousness never.
EVERY Judge listed above has had ties and relationships with shady characters or characters of ill repute - and probably still does.
Enter PCII and a Quick Lesson on What It Is…
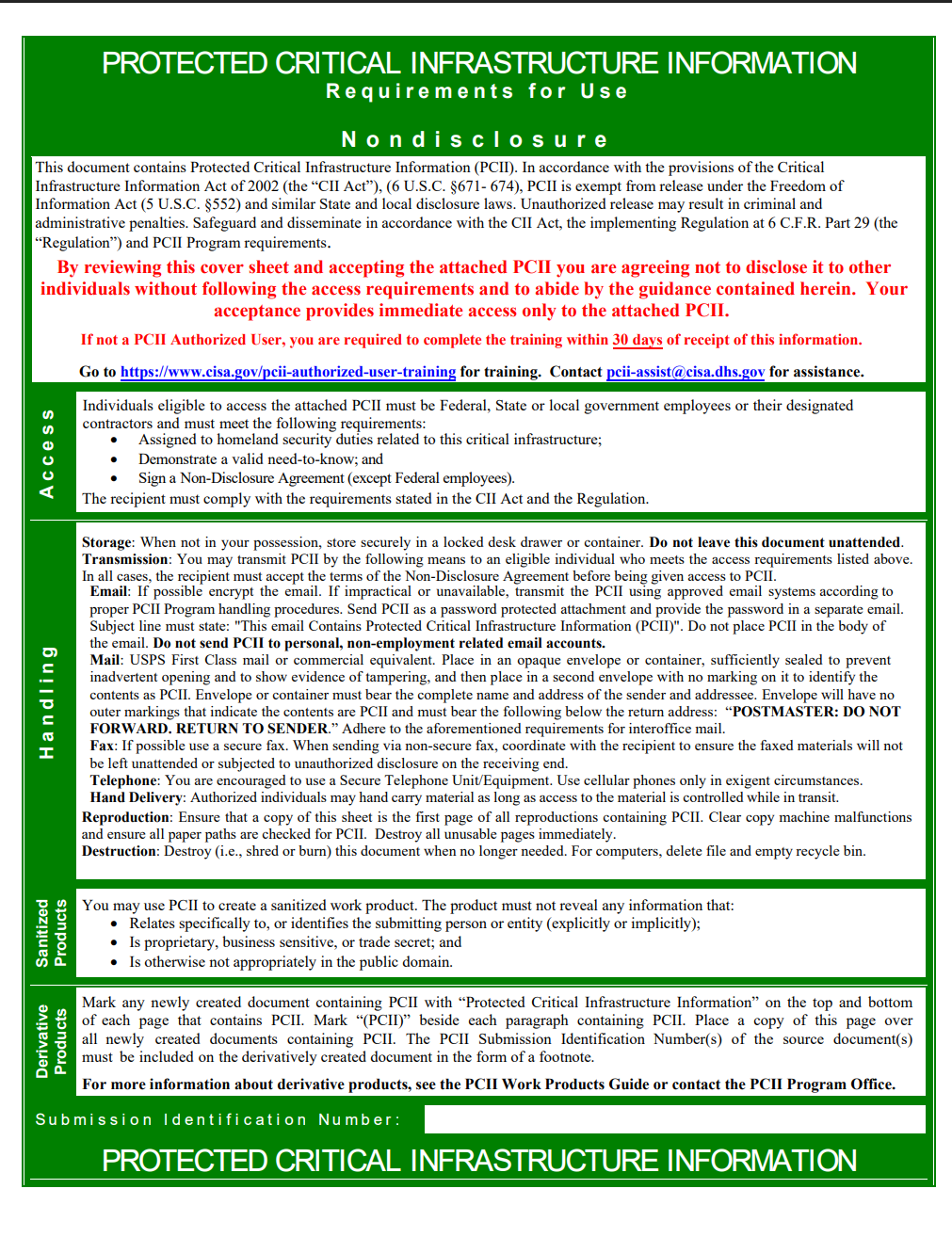
Protected Critical Infrastructure Information (PCII) is validated Critical Infrastructure Information (CII) that has been voluntarily submitted to the Department of Homeland Security (DHS) through CISA.
This information includes details about the security of critical infrastructure and protected systems, such as documents, records, or other information concerning threats, vulnerabilities, and operational experiences.
The PCII Program aims to reduce the United States' vulnerability to terrorism by encouraging the submission of CII while safeguarding it from unauthorized disclosure.
The CII Act of 2002 and its implementing regulation, 6 CFR part 29, establish procedures for handling this information, ensuring its protection from public disclosure under laws like the Freedom of Information Act (FOIA), its use in civil litigation, and its use for regulatory purposes.
Information submitted for PCII protection must relate to the security of critical infrastructure, be voluntarily provided, not customarily available in the public domain, and not submitted in place of complying with regulatory requirements.
Once validated as PCII, the information is marked with “PROTECTED CRITICAL INFRASTRUCTURE INFORMATION” in headers and footers and includes a green cover sheet outlining protection requirements.
The PCII Program Office or its designees are the only entities authorized to mark information as PCII and assign a submission identification number.
This protection remains in effect until the PCII Program Office determines the information no longer qualifies for protection or the submitter requests its removal.
DHS and other federal, state, and local government analysts utilize PCII to analyze and secure critical infrastructure and protected systems, identify vulnerabilities, develop risk assessments, and enhance preparedness, resilience, and recovery measures.
IF you want to drill down even deeper, the CISA site is available here…
If you want to follow an excellent resource on CISA, especially cybersecurity, look up Mike Benz - he is everywhere.
ICYMI - the Cybersecurity and Infrastructure Security Agency (CISA) is a component of the United States Department of Homeland Security (DHS).
To access any of their documentation, all one needs to be is any government employee and follow these instructions…
Recently, the Durham Annex report showed how the seditious George Soros, Hillary Clinton, and Barack Obama subverted our Constitutional for of government via unlawful means (election fraud via RICO enterprise). [link / archive]
All this continues on The Miami Independent…
PROTECTED CRITICAL INFRASTRUCTURE, FRAUD, and TREASON
by Chris Gleason, August 10, 2025
In Chris Gleason’s article, you will see…
PDFs of the emails corroborating the unlawful means
You will discover that the RUSSIAN COLLUSION HOAX has been exposed for what it is: as part of the coup, Obama, Hillary, and their co-conspirators designated our elections as “CRITICAL INFRASTRUCTURE.”
PCII fraudulent concealment, false claims, official misconduct, HAVA, and more…
The author outlines the key implications based on relevant U.S. laws, including those governing PCII misuse, conspiracy, election integrity, and judicial conduct.
NOTE: Outcomes will depend on jurisdiction, evidence of intent, and specific facts, but …
… this scenario aligns with patterns seen in post-2020 election litigation, where unsubstantiated fraud claims were rejected,
and attempts to obstruct access to records were scrutinized.



We're watching a long drawn out act of pathetic morons that can't win ever without cheating worse than a pox upon thee not meeeeee
EVERYONE OF THEM SHOULD BE DISSBARRED AND KICKED OFF OF THE BENCH IMMEDIATELY! 🇺🇸 USA 🇺🇸